Enterprise security teams have a growing visibility problem, and it lives inside the browser. The 2026 State of Browser Security Report, published by Keep Aware, finds that browsers have become the primary execution layer for modern work while remaining one of the least protected surfaces in most enterprise environments.
The report draws on 2025 telemetry to document how AI tools, SaaS activity, and sensitive data handling have converged inside browser sessions, largely out of reach from conventional security controls.
AI Tools Are Now Standard, Governance Is Not
Generative AI moved from experimental to routine inside the enterprise during 2025. Keep Aware’s data shows that 41% of end users interacted with at least one AI web tool over the past year, with the average employee using 1.91 AI tools per person.
Usage patterns reveal a governance gap. While many organizations formally approve specific AI platforms, employees frequently access those same tools through personal accounts, bypassing enterprise oversight entirely. AI-native browsers and embedded copilots now handle drafting, coding, research, and data analysis, all within browser sessions that traditional security architectures were never designed to inspect.
The risk is not just about which tools employees use. Employees are actively pasting internal documents, source code, financial data, and regulated information directly into AI interfaces, often without any security visibility into those actions.
Sensitive Data Is Leaking Through Trusted Applications
One of the report’s sharper findings challenges a common security assumption: that enforcing sanctioned applications is enough to control data exposure. The data says otherwise.
During a one-month snapshot of authenticated sessions, 54% of sensitive inputs to web applications were sent through corporate accounts, while 46% traveled through personal accounts or unverified work accounts. Sensitive uploads were concentrated in widely trusted platforms including SharePoint, Google services, Slack, and Box, but frequently accessed under personal identities that fall outside enterprise governance.
This finding shifts the frame. The risk is less about which application an employee opens and more about which identity they use when they open it. Application-layer blocking cannot solve that problem. Traditional data loss prevention tools built around email gateways, network inspection, or endpoint file monitoring have no mechanism to catch typed inputs or pasted data inside an active browser session.
Attackers Have Already Made the Move
As organizations reinforced email and endpoint defenses, attackers redirected their efforts into the browser. Keep Aware’s 2025 observations break down the primary attack categories:
- 29% — Phishing
- 19% — Suspicious or malicious browser extensions
- 17% — Social engineering
The phishing data carries an especially notable detail: the domains used in these attacks carried a median age of over 18 years. That means reputation-based and domain-age filtering, common staples of legacy security stacks, are increasingly ineffective against current tactics.
The Architecture Gap Is Widening
Most enterprise security stacks still treat the browser as an extension of network or endpoint controls. The 2026 report argues that framing is outdated. The browser now reads data, generates content, executes workflows, and acts on behalf of users in real time. In many organizations it has effectively become the operating system for daily work.
Security strategies built before that shift can no longer account for where the most consequential activity actually occurs. The browser is where AI-driven work happens. It is also, according to this data, where visibility has consistently failed to keep pace.
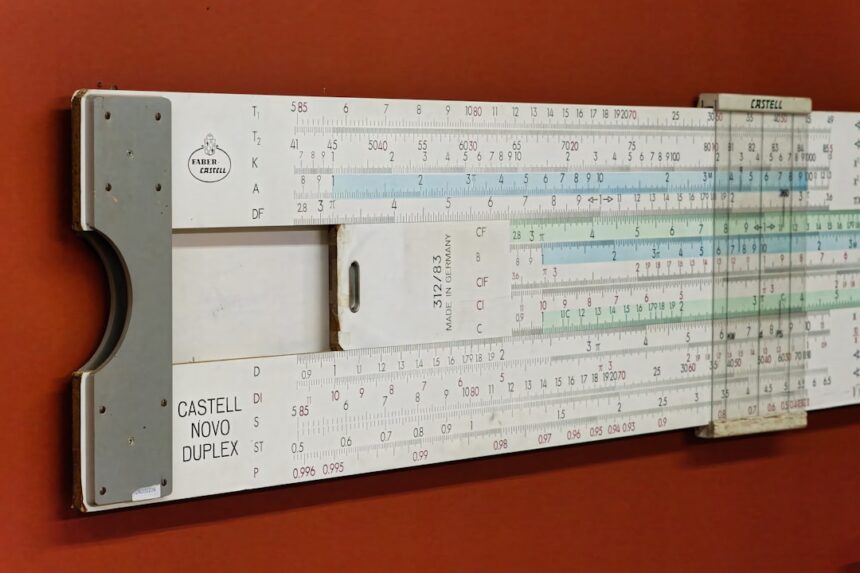
Photo by Eric Prouzet on Unsplash
This article is a curated summary based on third-party sources. Source: Read the original article