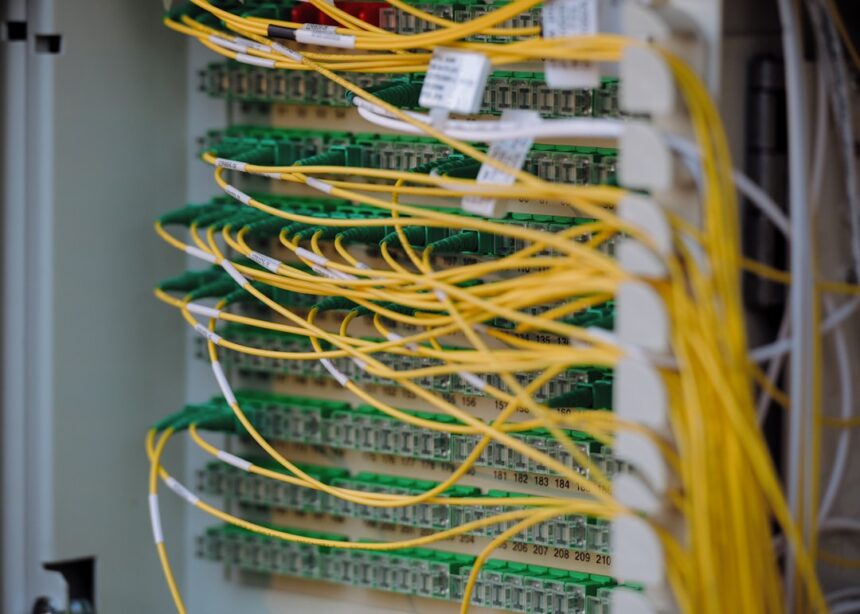
Telecom infrastructure has become a consistent target for China-linked espionage operations, with Salt Typhoon‘s documented intrusions into carrier networks setting a broader pattern. A newly detailed campaign extends that picture into South America, deploying tooling that is distinct but operationally adjacent.
Cisco Talos is tracking the activity under the cluster designation UAT-9244, which it describes as closely associated with FamousSparrow — a group assessed to share tactical overlaps with Salt Typhoon. According to the report, the two clusters share a targeting footprint focused on telecommunications providers, though Talos states there is no conclusive evidence directly linking UAT-9244 to Salt Typhoon. The campaign has been active since 2024, hitting both Windows and Linux systems as well as network edge devices.
Three previously undocumented implants drive the operation. TernDoor targets Windows hosts through DLL side-loading, using the legitimate executable wsprint.exe to launch a rogue DLL — BugSplatRc64.dll — that decrypts and executes the final payload in memory. A variant of Crowdoor, itself derived from SparrowDoor, the backdoor has been in use by UAT-9244 since at least November 2024. It establishes persistence via scheduled tasks or Registry Run keys, embeds a Windows driver to manage processes, and communicates with a command-and-control server to run arbitrary commands, read and write files, and collect system information. It also performs an injection check to confirm it is running inside msiexec.exe before decoding its C2 configuration.
A Linux Backdoor Built for Embedded Systems
PeerTime — also known as angrypeer — is an ELF backdoor compiled for ARM, AARCH, PPC, and MIPS architectures, allowing it to infect a range of embedded systems. Deployed via a shell script alongside an instrumentor binary, the loader checks for the presence of Docker on the compromised host before executing the final payload entirely in memory. Talos researchers Asheer Malhotra and Brandon White note that the instrumentor binary contains debug strings in Simplified Chinese, pointing to Chinese-speaking developers. The backdoor comes in two versions — one written in C/C++ and a newer variant in Rust — and uses the BitTorrent protocol to retrieve C2 information and download files from peers, while also renaming itself as a benign process to sidestep detection.
Edge Devices Weaponized as Scanning Infrastructure
The third implant, BruteEntry, is installed on network edge devices and converts them into mass-scanning proxy nodes inside an Operational Relay Box. A shell script drops two Golang-based components: an orchestrator that delivers BruteEntry, which then contacts a C2 server to obtain target IP addresses for brute-force attacks against Postgres, SSH, and Tomcat servers. Successful credential logins are reported back to the C2; failed attempts return the message “All credentials tried.”
The exact initial access vector remains unconfirmed. Talos notes the threat actor has previously exploited systems running outdated versions of Windows Server and Microsoft Exchange Server, dropping web shells for follow-on access — a technique consistent with opportunistic exploitation of unpatched edge infrastructure.
Photo by Albert Stoynov on Unsplash
This article is a curated summary based on third-party sources. Source: Read the original article