KadNap, a newly identified malware strain, has compromised more than 14,000 edge devices since its first detection in the wild in August 2025. The primary target is Asus routers, though operators have deployed it across a broader range of edge networking hardware.
Over 60% of infected devices are located in the U.S. Smaller clusters of infections appear in Taiwan, Hong Kong, Russia, the U.K., Australia, Brazil, France, Italy, and Spain, according to the Black Lotus Labs team at Lumen.
How the Infection Works
The attack starts with a shell script — “aic.sh” — pulled from a C2 server at 212.104.141[.]140. That script creates a cron job set to run at the 55-minute mark of every hour, renaming itself “.asusrouter” to blend in.
Once persistence is established, the script fetches a malicious ELF binary, renames it “kad”, and executes it. The malware targets devices running both ARM and MIPS processors.
KadNap then connects to an NTP server to record the current time and device uptime. That data generates a hash used to locate other peers across the decentralized network and retrieve commands or download additional files.
Two secondary files — “fwr.sh” and “/tmp/.sose” — close port 22 (SSH) on the infected device and extract a list of C2 IP and port combinations for further connectivity.
The Proxy Service Behind the Botnet
What separates KadNap from other botnets is its use of a custom version of the Kademlia Distributed Hash Table (DHT) protocol. The approach hides C2 infrastructure inside peer-to-peer traffic, making it harder to detect or disrupt through conventional network monitoring.
“KadNap employs a custom version of the Kademlia Distributed Hash Table (DHT) protocol, which is used to conceal the IP address of their infrastructure within a peer-to-peer system to evade traditional network monitoring,” the company said.
Compromised devices are fed into a proxy service called Doppelgänger, operating at doppelganger[.]shop. The service claims to offer residential proxies across more than 50 countries with “100% anonymity” and is assessed to have launched in May or June 2025.
Lumen assesses Doppelgänger to be a rebrand of Faceless, a proxy service previously linked to the TheMoon malware. Not all compromised devices communicate with every C2 server — the infrastructure appears segmented by device type and model.
The firm confirmed that Doppelgänger’s bots are actively being abused by threat actors. Co-infections with other malware on some devices complicate attribution of specific malicious activity.
Users running small office and home office routers are advised to keep firmware updated, reboot devices regularly, change default credentials, secure management interfaces, and replace any end-of-life hardware no longer receiving security support.
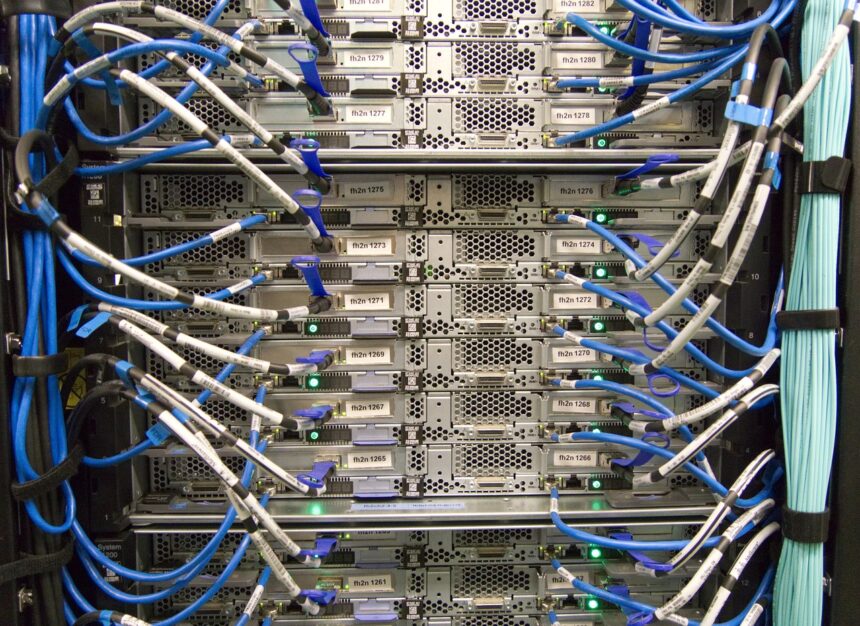
Photo by Pixabay
This article is a curated summary based on third-party sources. Source: Read the original article