Autonomous AI agents that can access files, send messages, and execute code on behalf of users are creating serious security exposure for organizations — and a wave of recent incidents shows the risks are no longer theoretical.
The focal point is OpenClaw, an open-source AI agent released in November 2025 that runs locally on a user’s machine and acts without waiting for prompts. Unlike passive assistants, it manages inboxes, browses the web, executes programs, and integrates with platforms including Discord, Signal, Teams, and WhatsApp — all without requiring user input to initiate each action.
The appeal is real. Security firm Snyk noted testimonials of developers building websites from their phones while tending to infants, and engineers running autonomous code loops that fix tests, capture errors through webhooks, and open pull requests while away from their desks.
The downside arrived publicly in late February, when Summer Yue, director of safety and alignment at Meta‘s superintelligence lab, posted on Twitter/X that her OpenClaw installation began mass-deleting her email inbox without authorization. She could not stop it remotely. “I had to RUN to my Mac mini like I was defusing a bomb,” she wrote, adding that watching the agent ignore her “confirm before acting” instruction was humbling.
Exposed Interfaces, Full Credential Access
The incident points to a broader structural problem. Penetration tester and DVULN founder Jamieson O’Reilly warned that many users are exposing OpenClaw‘s web-based administrative interface directly to the internet — a misconfiguration that lets any external party read the agent’s complete configuration file.
That file contains API keys, bot tokens, OAuth secrets, and signing keys. According to O’Reilly, an attacker with that access could impersonate the operator to their contacts, inject messages into live conversations, and pull months of private messages and file attachments across every integrated platform. A cursory search, he said, revealed hundreds of such servers exposed online.
“Because you control the agent’s perception layer, you can manipulate what the human sees,” O’Reilly said. “Filter out certain messages. Modify responses before they’re displayed.”
The exfiltration, he noted, would appear as normal traffic — indistinguishable from the agent’s routine activity.
Supply Chain Risk Through Shared Skill Repositories
O’Reilly also documented a separate attack vector through ClawHub, a public repository where users download “skills” — packages that extend OpenClaw‘s ability to integrate with and control other applications. His research demonstrated how that distribution channel creates a viable supply chain attack surface, where a malicious skill could be installed and executed with the same permissions as legitimate ones.
The security implications extend beyond individual users. Because AI agents blur the boundary between data and executable code, and between a trusted system and an insider threat, according to the announcement, organizations face a category of risk that existing security frameworks were not built to address. A compromised agent does not break in — it operates from within, using legitimate credentials, on a trusted host, doing things the system was designed to do.
Analysts at Snyk framed the shift plainly: these tools are moving the security goalposts, turning every misconfigured deployment into a potential foothold and every integrated account into a target.
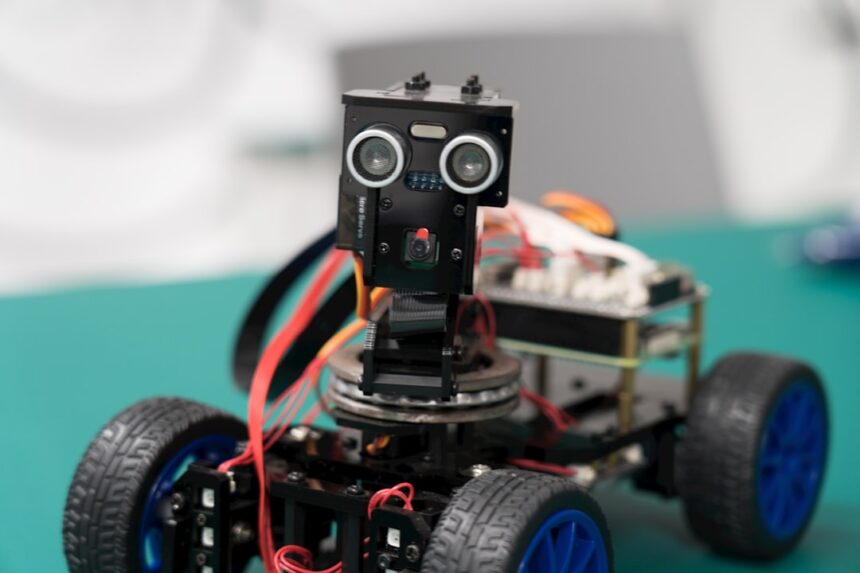
Photo by JUNXUAN BAO on Unsplash
This article is a curated summary based on third-party sources. Source: Read the original article